 |  |
|  | |||||||
| Network Security Management Lecture sharing portion for Network Security Management, Sir Moizuddin |
 |
| | Thread Tools | Search this Thread | Rating:  | Display Modes |
|
#1
| ||||
| ||||
| Overview "Distance Vector" and "Link State" are terms used to describe routing protocols which are used by routers to forward packets between networks. The purpose of any routing protocol is to dynamically communicate information about all network paths used to reach a destination and to select the from those paths, the best path to reach a destination network. The terms distance vector and link state are used to group routing protocols into two broad categories based on whether the routing protocol selects the best routing path based on a distance metric (the distance) and an interface (the vector), or selects the best routing path by calculating the state of each link in a path and finding the path that has the lowest total metric to reach the destination. DISTANCE VECTOR
Common distance vector routing protocols include:
Link State protocols track the status and connection type of each link and produces a calculated metric based on these and other factors, including some set by the network administrator. Link state protocols know whether a link is up or down and how fast it is and calculates a cost to 'get there'. Since routers run routing protocols to figure out how to get to a destination, you can think of the 'link states' as being the status of the interfaces on the router. Link State protocols will take a path which has more hops, but that uses a faster medium over a path using a slower medium with fewer hops. Because of their awareness of media types and other factors, link state protocols require more processing power (more circuit logic in the case of ASICs) and memory. Distance vector algorithms being simpler require simpler hardware. A Comparison: Link State vs. Distance Vector See Fig. 1-1 below. If all routers were running a Distance Vector protocol, the path or 'route' chosen would be from A B directly over the ISDN serial link, even though that link is about 10 times slower than the indirect route from A C D B. A Link State protocol would choose the A C D B path because it's using a faster medium (100 Mb ethernet). In this example, it would be better to run a Link State routing protocol, but if all the links in the network are the same speed, then a Distance Vector protocol is better. ================================================== There are two major classes of routing protocol: distance vector and link-state. It's easy to remember which protocols belong to either class, but comprehending their differences between the two classes takes a bit more effort. Distance vector routing is so named because it involves two factors: the distance, or metric, of a destination, and the vector, or direction to take to get there. Routing information is only exchanged between directly connected neighbors. This means a router knows from which neighbor a route was learned, but it does not know where that neighbor learned the route; a router can't see beyond its own neighbors. This aspect of distance vector routing is sometimes referred to as "routing by rumor." Measures like split horizon and poison reverse are employed to avoid routing loops. Link-state routing, in contrast, requires that all routers know about the paths reachable by all other routers in the network. Link-state information is flooded throughout the link-state domain (an area in OSPF or IS-IS) to ensure all routers posess a synchronized copy of the area's link-state database. From this common database, each router constructs its own relative shortest-path tree, with itself as the root, for all known routes. Consider the following topology. 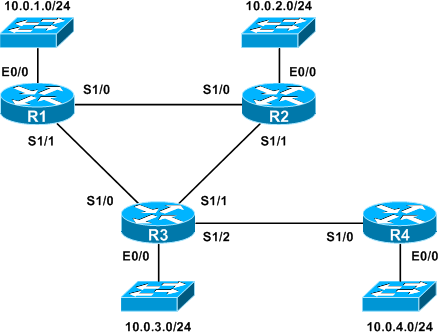 Distance Vector If we were to run a distance vector routing protocol like RIP or EIGRP on this topology, here's how R1 would see the network, assuming each link has a metric of 1 (locally connected routes have been omitted):   Link-State Now, let's look at the same topology running a link-state routing protocol (in a single area). Because each router records the state of all links in the area, each router can construct a shortest-path tree from itself to all known destinations. Here's what R1's tree would look like:  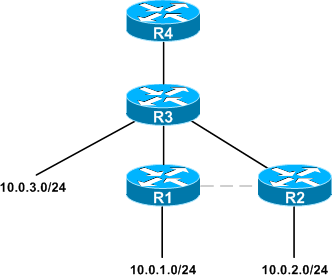
__________________ (¯`v´¯) `*.¸.*` ¸.*´¸.*´¨) ¸.*´¨) (¸.*´ (¸.Bzu Forum  Don't cry because it's over, smile because it happened Don't cry because it's over, smile because it happened  |
 |
| Tags |
| distance, linkstate, vector, versus |
« Previous Thread
|
Next Thread »
| Currently Active Users Viewing This Thread: 1 (0 members and 1 guests) | |
| |
 Similar Threads
Similar Threads | ||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| LOVE versus MARRIAGE | usman_latif_ch | Quotes | 0 | 13-04-2009 04:41 PM |
Almuslimeen.info | BZU Multan | Dedicated server hosting
Note: All trademarks and copyrights held by respective owners. We will take action against any copyright violation if it is proved to us.
All times are GMT +5. The time now is 08:31 AM.
Powered by vBulletin® Version 3.8.2
Copyright ©2000 - 2026, Jelsoft Enterprises Ltd.
Copyright ©2000 - 2026, Jelsoft Enterprises Ltd.


 .BZU.
.BZU.





 Linear Mode
Linear Mode

